Computer Security - Quick Guide
In this tutorial, we will treat the concept of Computer Security which can be a laptop, a workstation, a server or a network device. This tutorial is done mainly for people that are within the IT industry who are IT specialists, System administrators, Security administrators.
Why Security?
Cyberspace (internet, work environment, intranet) is becoming a dangerous place for all organizations and individuals to protect their sensitive data or reputation. This is because of the numerous people and machines accessing it. It is important to mention that the recent studies have shown a big danger is coming from internal threats or from disappointed employee. Another internal threat is that information material can be easy accessible over the intranet.
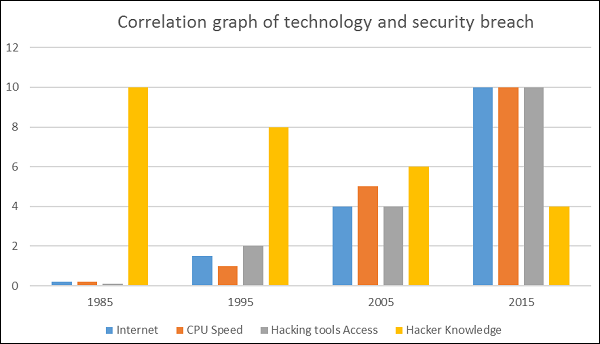
One important indicator is the IT skills of a person that wants to hack or to breach your security has decreased but the success rate of it has increased, this is because of three main factors −
- Hacking tools that can be found very easily by everyone just by googling and they are endless.
- Technology with the end-users has increased rapidly within these years, like internet bandwidth and computer processing speeds.
- Access to hacking information manuals.
All this can make even a school boy with the curiosity, a potential hacker for your organization.
Since locking down all networks is not an available option, the only response the security managers can give is to harden their networks, applications and operating systems to a reasonable level of safety, and conducting a business disaster recovery plan.
The following graph gives us a basic idea.
What to Secure?
Let’s see this case, you are an IT administrator in a small company having two small servers staying in a corner and you are very good at your job. You are doing updates regularly, setting up firewalls, antiviruses, etc. One day, you see that the organization employees are not accessing the systems anymore. When you go and check, you see the cleaning lady doing her job and by mistake, she had removed the power cable and unplugged the server.
What I mean by this case is that even physical security is important in computer security, as most of us think it is the last thing to take care of.
Now let’s go directly to the point of what all to secure in a computer environment −
- First of all, is to check the physical security by setting control systems like motion alarms, door accessing systems, humidity sensors, temperature sensors. All these components decrease the possibility of a computer to be stolen or damaged by humans and environment itself.
- People having access to computer systems should have their own user id with password protection.
- Monitors should be screen saver protected to hide the information from being displayed when the user is away or inactive.
- Secure your network especially wireless, passwords should be used.
- Internet equipment as routers to be protected with password.
- Data that you use to store information which can be financial, or non-financial by encryption.
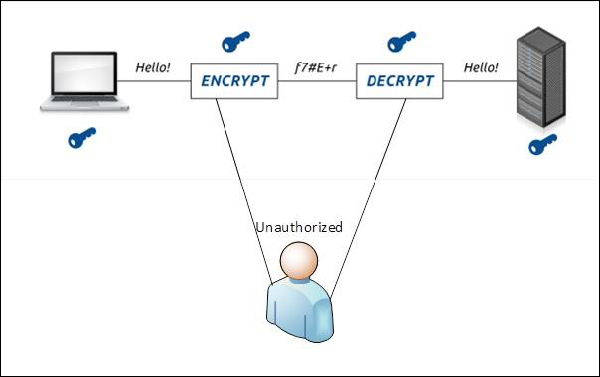
- Information should be protected in all types of its representation in transmission by encrypting it.
Benefits of Computer Security Awareness
Do you know in all this digital world, what is the biggest hole or the weakest point of the security?
Answer. It is us, humans.
Most of the security breaches come from uninformed and untrained persons which give information to a third party or publish data in Internet without knowing the consequences.
See the following scenario which tells us what employees might end up doing without computer security awareness −
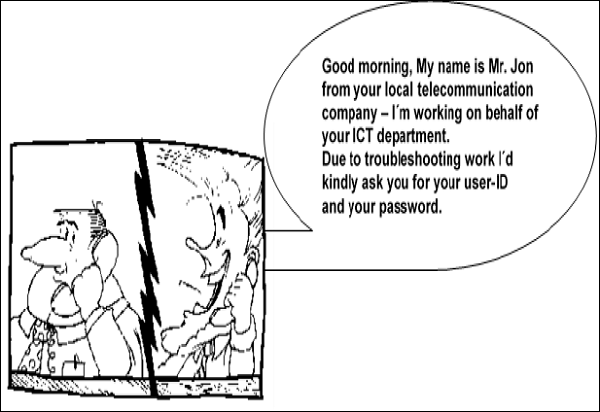
So the benefits of computer security awareness are obvious as it directly minimizes the potential of you being hacked off your identity, your computer, your organization.
Potential Losses due to Security Attacks
The potential loses in this cyberspace are many even if you are using a single computer in your room. Here, I will be listing some examples that have a direct impact on you and on others −
- Losing you data − If your computer has been hacked or infected, there is a big chance that all your stored data might be taken by the attacker.
- Bad usage of your computer resources − This means that your network or computer can go in overload so you cannot access your genuine services or in a worst case scenario, it can be used by the hacker to attack another machine or network.
- Reputation loss − Just think if your Facebook account or business email has been owned by a social engineering attack and it sends fake information to your friends, business partners. You will need time to gain back your reputation.
- Identity theft − This is a case where your identity is stolen (photo, name surname, address, and credit card) and can be used for a crime like making false identity documents.
Basic Computer Security Checklist
There are some basic things that everyone of us in every operating system need to do −
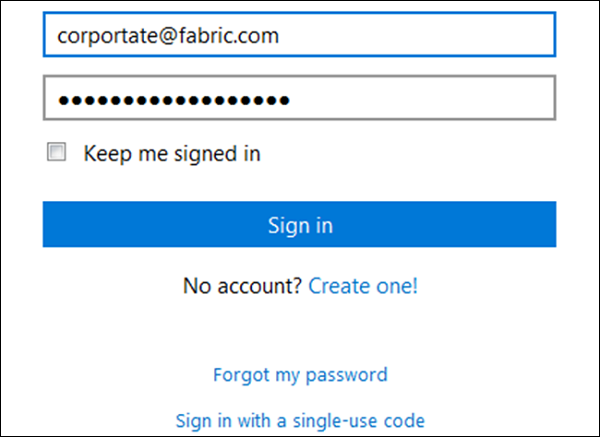
- Check if the user is password protected.
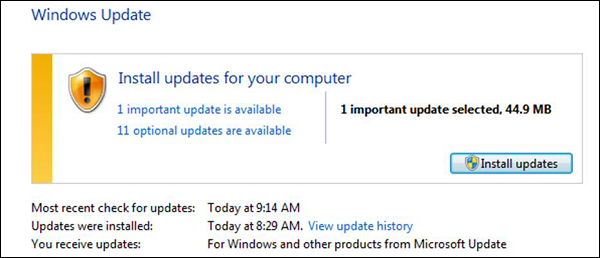
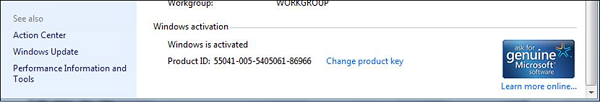
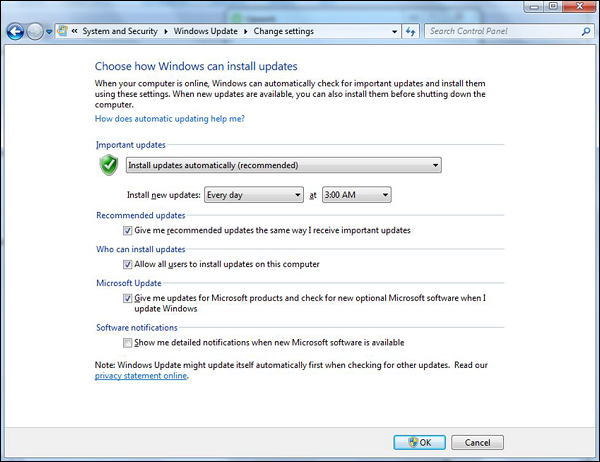
- Check if the operating system is being updated. In my case, I did a screenshot of my laptop which is a Windows 7.
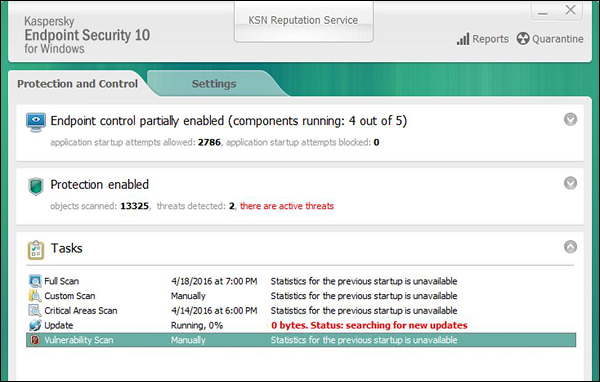
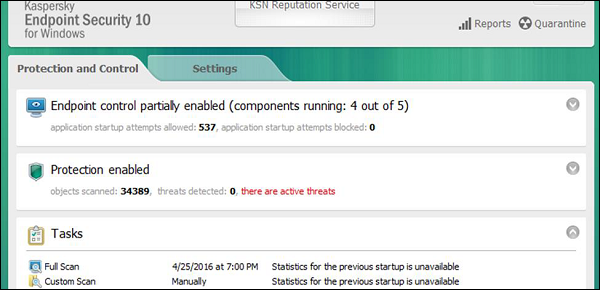
- Check if the antivirus or antimalware is installed and updated. In my case, I have a Kaspersky antivirus being updated.
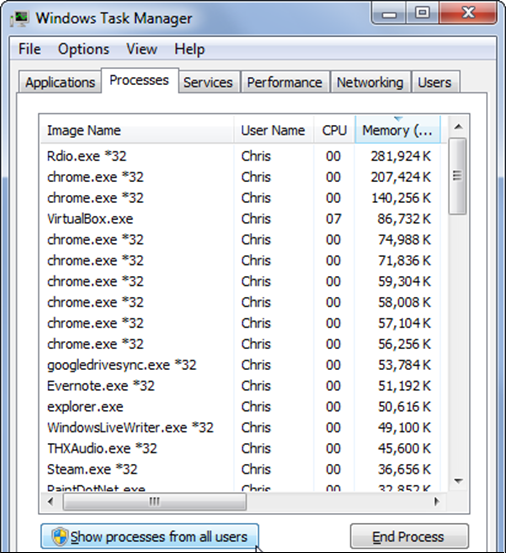
- Check for the unusual services running that consumes resources.
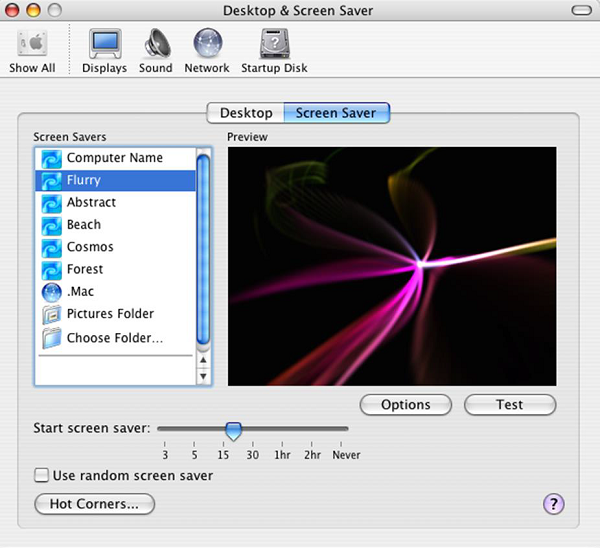
- Check if your monitor is using a screen saver.
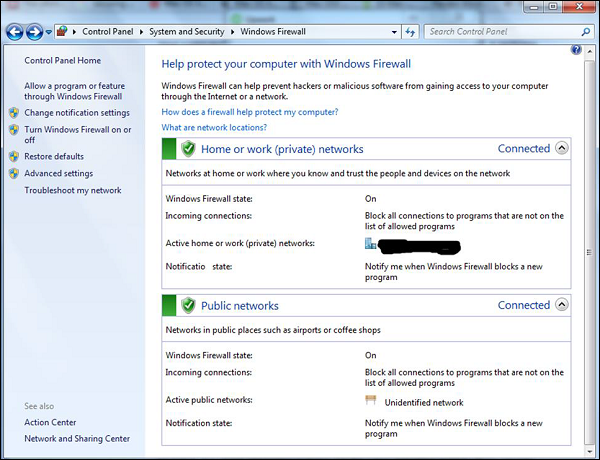
- Check if the computer firewall is on or not.
- Check if you are doing backups regularly.
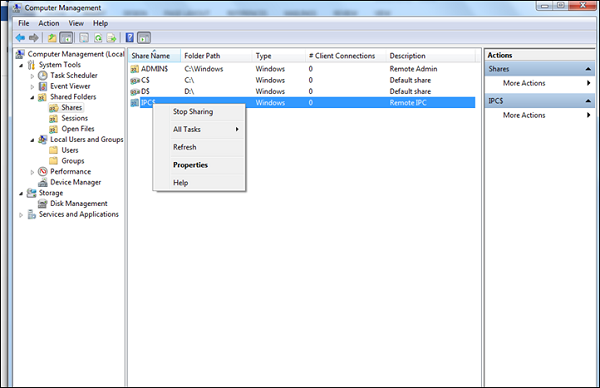
- Check if there are shares that are not useful.
- Check if your account has full rights or is restricted.
- Update other third party software’s.
Computer Security - Elements
The general state in Computer Security has the ability to detect and prevent attacks and to be able to recover. If these attacks are successful as such then it has to contain the disruption of information and services and check if they are kept low or tolerable.
Different Elements in Computer Security
In order to fulfil these requirements, we come to the three main elements which are confidentiality, integrity, and availability and the recently added authenticity and utility.
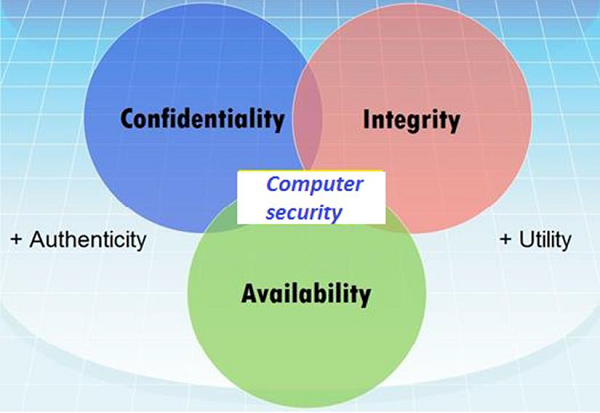
Confidentiality
Confidentiality is the concealment of information or resources. Also, there is a need to keep information secret from other third parties that want to have access to it, so just the right people can access it.
Example in real life − Let’s say there are two people communicating via an encrypted email they know the decryption keys of each other and they read the email by entering these keys into the email program. If someone else can read these decryption keys when they are entered into the program, then the confidentiality of that email is compromised.
Integrity
Integrity is the trustworthiness of data in the systems or resources by the point of view of preventing unauthorized and improper changes. Generally, Integrity is composed of two sub-elements – data-integrity, which it has to do with the content of the data and authentication which has to do with the origin of the data as such information has values only if it is correct.
Example in real life − Let’s say you are doing an online payment of 5 USD, but your information is tampered without your knowledge in a way by sending to the seller 500 USD, this would cost you too much.
In this case cryptography plays a very major role in ensuring data integrity. Commonly used methods to protect data integrity includes hashing the data you receive and comparing it with the hash of the original message. However, this means that the hash of the original data must be provided in a secure way.
Availability
Availability refers to the ability to access data of a resource when it is needed, as such the information has value only if the authorized people can access at right time. Denying access to data nowadays has become a common attack. Imagine a downtime of a live server how costly it can be.
Example in real life − Let’s say a hacker has compromised a webserver of a bank and put it down. You as an authenticated user want to do an e-banking transfer but it is impossible to access it, the undone transfer is a money lost for the bank.
Computer Security - Terminologies
In this chapter, we will discuss about the different terminology used in Computer Security.
- Unauthorized access − An unauthorized access is when someone gains access to a server, website, or other sensitive data using someone else's account details.
- Hacker − Is a Person who tries and exploits a computer system for a reason which can be money, a social cause, fun etc.
- Threat − Is an action or event that might compromise the security.
- Vulnerability − It is a weakness, a design problem or implementation error in a system that can lead to an unexpected and undesirable event regarding security system.
- Attack − Is an assault on the system security that is delivered by a person or a machine to a system. It violates security.
- Antivirus or Antimalware − Is a software that operates on different OS which is used to prevent from malicious software.
- Social Engineering − Is a technique that a hacker uses to stole data by a person for different for purposes by psychological manipulation combined with social scenes.
- Virus − It is a malicious software that installs on your computer without your consent for a bad purpose.
- Firewall − It is a software or hardware which is used to filter network traffic based on rules.
Computer Security - Layers
In Computer Security, layers is a well-known practice which was taken from military techniques. The aim of this is to exhaust the attacker when he succeeds to penetrate the first layer of security by finding a hole, then he has to find a hole in the second layer and so on, until he arrives at the destination if he succeeds.
Following is an image which explains about Layer Security.
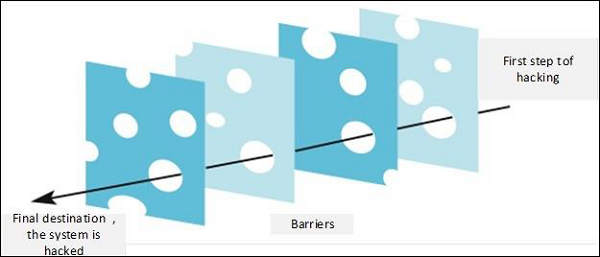
Let’s see the best practices in a Layer type of Security −
- Computer Application Whitelistening − The idea is to install just a restricted number of applications in your computers, which are useful as well as are genuine.
- Computer System Restore Solution − In case your computer is hacked and your files are damaged, you should have the possibility to again have access to your files. An example is Windows System Restore or Backup.
- Computer and Network Authentication − The data that is accessed over the network is best to be provided only to the authorized users. Use usernames and passwords!!!
- File, Disk and Removable Media Encryption − Generally a good practice is to encrypt hard disks or removable devices, the idea behind this is in case your laptop or your removable USB is stolen and it is plugged in another machine it cannot be read. A good tool for this is Truecrypt.
- Remote Access Authentication − Systems which are accessed over the network is best to be provided only to the authorized users. Use usernames and passwords!!!
- Network Folder Encryption − Again like the case of Network Authentication, if you have a network storage or a network folder shared, it is good to be encrypted to prevent any unauthorized user who is listening to the network to read the information.
- Secure Boundary and End-To-End Messaging − Nowadays email or instant messaging is widely spread and it is the number one tool to communicate. It is better that the communication to be encrypted between the end users, a good tool for this is PGP Encryption Tool.
Computer Security - Securing OS
In this section we will treat how to secure or harden (harden is another word used for securing OS) a workstation from the practical point of view and what are the steps to follow. We will treat the Windows OS and Mac OS X because most of the computers have this two operating systems, but the logic of securing is same for all the other operating systems like Linux or Android.
Guidelines for Windows OS Security
Following are the list of guidelines for Windows Operating System Security.
Use the licensed versions of Windows OS, not the cracked or pirated ones and activate them in order to take genuine updates.
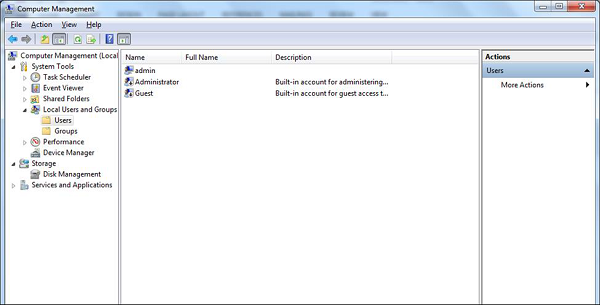
Disable Unused Users − To do this, Right Click on Computer – Manage – Local Users and Groups – Users, then disable those users that are not required. In my case, I disabled the Guest and Administrator users and I created a new non-default like Admin.
Disable unused shares − By default, Windows OS creates shares, please see the following screenshot. You have to disable them and to do this, you follow −
Right Click on My Computer – Manage – Shared Folders – Right Click Stop Sharing.
The next step is to take updates regularly for Windows OS. It is reccomended to do them automatically and periodically. To set this up, go to Control Panel – System and Security – Windows Updates – OK.
Put your Windows System Firewall up, this will block all the unauthorized services that make traffic. To set this up, go to Control Panel – System and Security – Windows Firewall.
Install a licensed antivirus and take updates, in the coming sections we will cover in detail about antiviruses. It is strongly recommended not to download from torrents and install cracked versions.
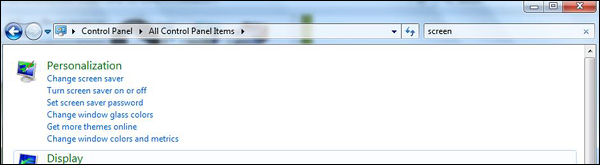
You should always Configure a password protected Screen Saver. To set this up, please follow this path −
Control Panel – All Control Panel Items – Personalize – Turn Screen Saver on or off – Check “On resume, display logon Screen”.
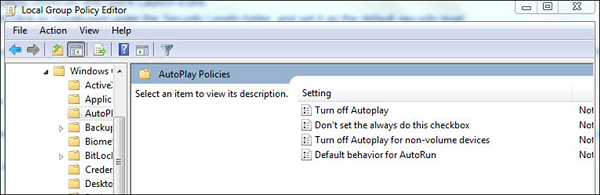
Disable Autoplay for Removable Media. This blocks the viruses to run automatically from removable devices.
To disable it go to – Start – on Search box type Edit Group Policy –Administrative Templates – Windows Components – Autoplay Policy – Turn off Autoplay – Enable – Ok.
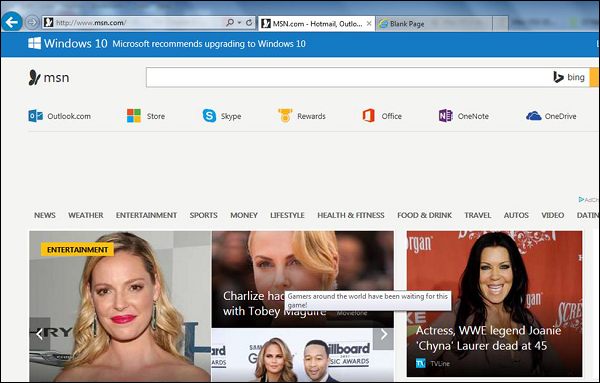
Install only trusted internet explorer browsers like Internet explorer, Chrome or Mozilla Firefox and then update them regularly. Missing the updates can lead to possible hacking.
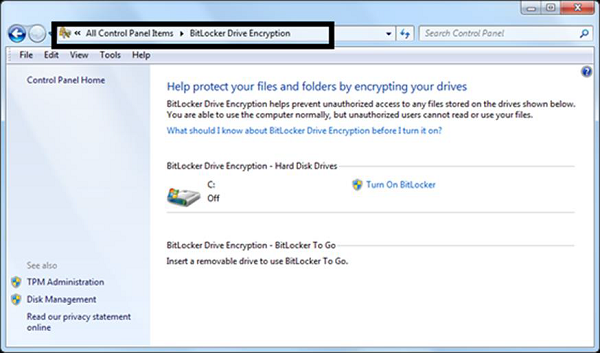
Enable the BitLocker Drive Encryption to encrypt hard drives, but it is only available in Windows & Ultimate and Upper Versions.
To enable it follow the path: Start – Control Panel – System and Security – BitLocker Drive Encryption.
Set Bios Password − This option differs based on different computer producers and we need to read manufacturer guidelines, this option secures your computer one layer upper in the OS.
Guidelines for Mac OS X Security
Following are the list of guidelines for Mac OS X Security.
Use licensed versions of Mac OS X and never use the cracked or pirated ones. Once installed, activate them in order to take up the genuine updates.
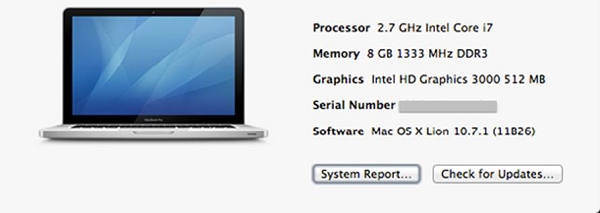
Set password for the root user and create a less privileged user. By default, the root user of the Mac OS X doesn’t have a password, so you have to put one and then create a user with less privilege for daily usage.
To set it up follow: Apple menu – System Preferences – Click Users & Groups

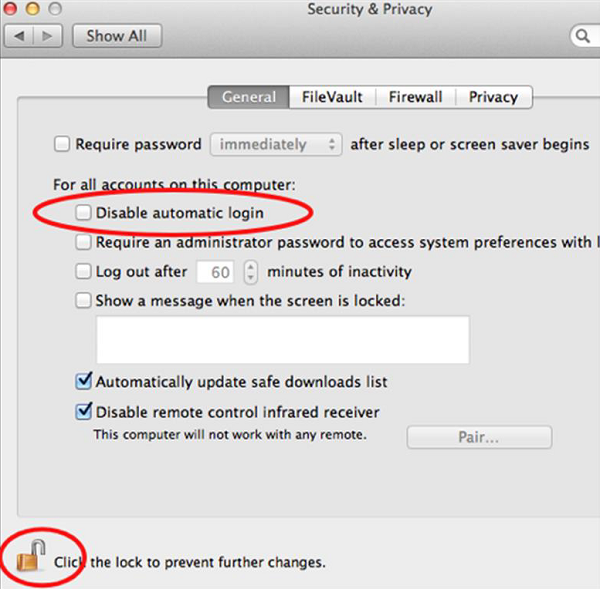
Disable Auto Logon − By default, the Mac OS X is configured to automatically logon the first administrative user that is created. Also it displays all valid usernames in the login windows.
To disable this, you have to: Open System Preferences – Accounts – User – Uncheck the Log in automatically – Click on Login Options (tab) – Set “Display Login Windows as” = Name and Password.
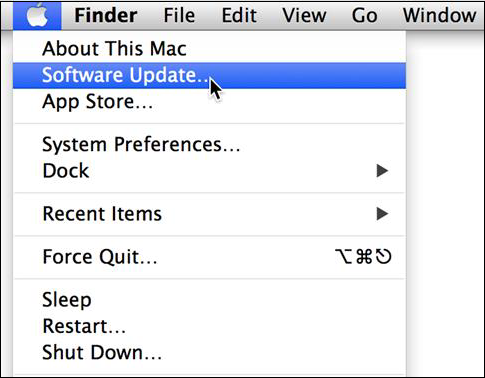
Update Mac OS X − In order to secure our systems, we need to take our updates and patches of Mac OS X.
To do so we follow this path: Click on System Preferences –Software Update – Change the default “weekly” to “daily” – Quit System Preferences.
You better do it weekly because it will not overload your networks, in case you have a large network.
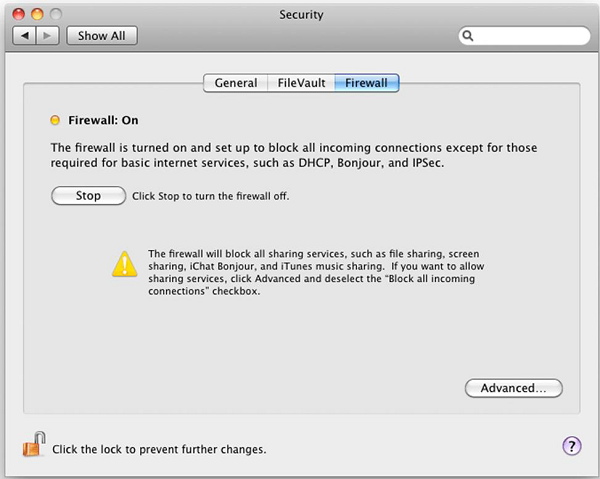
Put your Mac OS X system firewall up. The go to System Preferences – Sharing –Firewall – Click on Start.
Configure Screen saver password protected: To set this up, follow this path – System Preferences – Screen Effect – Activation – Set “Time until screen effect starts” = 5 Minutes – Set “Password to use when waking the screen effect” = use my user –account password. It is recommended to be less than 5 minutes.
Put Open Firmware password − Double click the application icon to open it. Click on the "Change" button to modify the security settings. If you are enabling the security features, enter a password into the – Password and Verify boxes. Click OK. Enter your System Administrator Account.











Very interesting and educative. Thank you for this wonderful post.
ReplyDelete